Typical strong authentication factors are not supported by Microsoft client encryption BitLocker. Enterprises need to stick to TPM-PIN authentication, password authentication or a quite unpopular USB stick authentication with a startup-key (a clear-text key file).
But there a many strong authentication mechanisms already deployed in enterprises that can be a perfect match for user authentication. These include smart cards, PKI crypto token, OTP token, smartphone authentication and multiple biometric identification options.
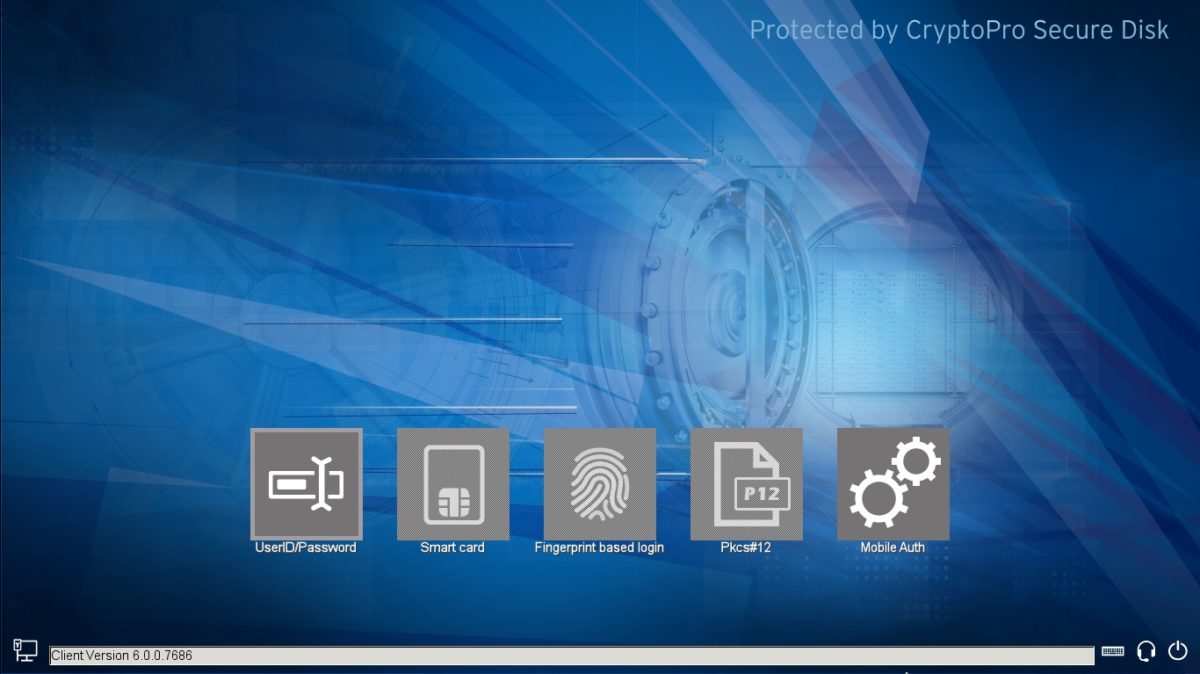
The Microsoft BitLocker add-on Secure Disk for BitLocker adds multiple multi-factor authentication methods to Microsoft BitLocker encryption including smart card authentication, PKI token authentication, biometric / fingerprint authentication, X.509 certificate support and smartphone app authentication in addition to the password or TPM based authentication methods.
All authentication methods are true user based identification methods and not machine authentication, as the Secure Disk for BitLocker pre-boot-authentication (PBA) supports multiple users per client.
Enhanced Multi-Factor BitLocker Protectors
This is a great enhancement to BitLocker standard two-factor authentication methods TPM+PIN and USB-stick and allows enterprises maximum flexibility in their security policies.
Clients can be configured to support different multi-factor authentication methods simultaneously, e.g. users can authenticate with their preferred smart card or fingerprint plus active directory password or smartphone authentication.
In large enterprise networks multi-factor authentication is widely used for administrator or support accounts on client machine.
Browser the full feature list of Secure Disk for BitLocker to see all strong authentication options for your BitLocker deployment.